Back to Basics: Secrets Management - バイリンガル字幕
Hello, welcome to another episode of Back to Basics.
My name is Hari Singeredi.
I'm a Solutions Architect here at AWS.
Today we are going to talk about managing and protecting secret information needed for your applications to perform its function.
These information could be your database passwords,
your IAM access keys, your SSH keys or any other information your application needs to perform its regular function.
Here I want to call out two best practices from AWS well architected framework security.
First one is store and retrieve these secure secrets.
Second one is audit and rotate these secrets securely and frequently.
Let's take you have an application that needs to communicate with the database.
So to open a connection to the database,
it needs database connection information, like the database server name, database port number, and secrets information like database username and database password.
So let's take a look at the architectural considerations first.
So there are a few things that you need to ask yourself.
First, where do you store these secrets securely?
Second, how does your application get access to these secrets?
Third, how often do you rotate these secrets?
And finally, when you rotate these secrets, how does your application know about the latest version of these secrets?
AWS Manager lets you store text in the protected data portion of the secret.
In this scenario, these could be your database username, password, and all other database correction information.
And data protection is a key security best practice, always encrypt data at rest.
So to achieve this, Secrets Manager encrypts the protected text of a secret by using AWS Key Management Service or KMS.
You can either use the default CMK for Secrets Manager or you can call it created CMK.
A common anti-pattern that we see is hard coding credentials in your application source code.
It's not a good idea because if somebody has access to your application source code, they now have access to your data.
AWS Secrets Manager allows for programmatic retrieval of secrets.
So to retrieve secrets, you simply replace plaintext secrets with code to pull in those secrets at runtime using Secrets Manager APIs.
You can also use AWS IAM permission policies to control access to your secret.
So in this scenario,
you can attach a policy to the role used by your application to give it read-only permissions on the database secrets.
And as I mentioned earlier, data protection is very important.
Secrets manager by default only accepts requests from hosts using open-standard TLS and perfect
forward secrecy and also ensures encryption of your secret while in transit.
Now, that storage and retrieval of the secret is set up, let's take a look at the second
security best practice, which is audit and rotate the secrets periodically.
Periodic rotation of secrets is really important from a security perspective.
If you don't change your secrets for a long period of time, the secrets become more likely to be compromised.
As a security best practice, we recommend that you regularly rotate your secrets.
You can configure Secrets Manager to automatically rotate without any manual intervention and on a specified schedule.
you.
Secrets uses AWS Lambda functions to rotate the credentials.
Secrets Manager out of the box comes fully configured and ready-to-use rotation support for Amazon RDS databases,
Amazon Aurora, Amazon DocumentDB, and Amazon Redshift.
If you need to rotate credentials for any other service than what I just mentioned,
you can also define and implement rotation using a custom Since your application is already configured to pull the latest credentials,
it will get the latest credentials next time it tries to access the database.
So if we take a look at the high-level overview of the pattern, you store your credentials in Secrets Manager.
Secrets Manager will take care of the rotation and maintaining the latest set of credentials for you.
always pulls the latest set of credentials from Secrets Manager at runtime.
And of this is happening securely and automatically.
There you have it.
Check out the resources below for more details and thanks for tuning in.
さらなる機能をアンロック
Trancy拡張機能をインストールすると、AI字幕、AI単語定義、AI文法分析、AIスピーチなど、さらなる機能をアンロックできます。
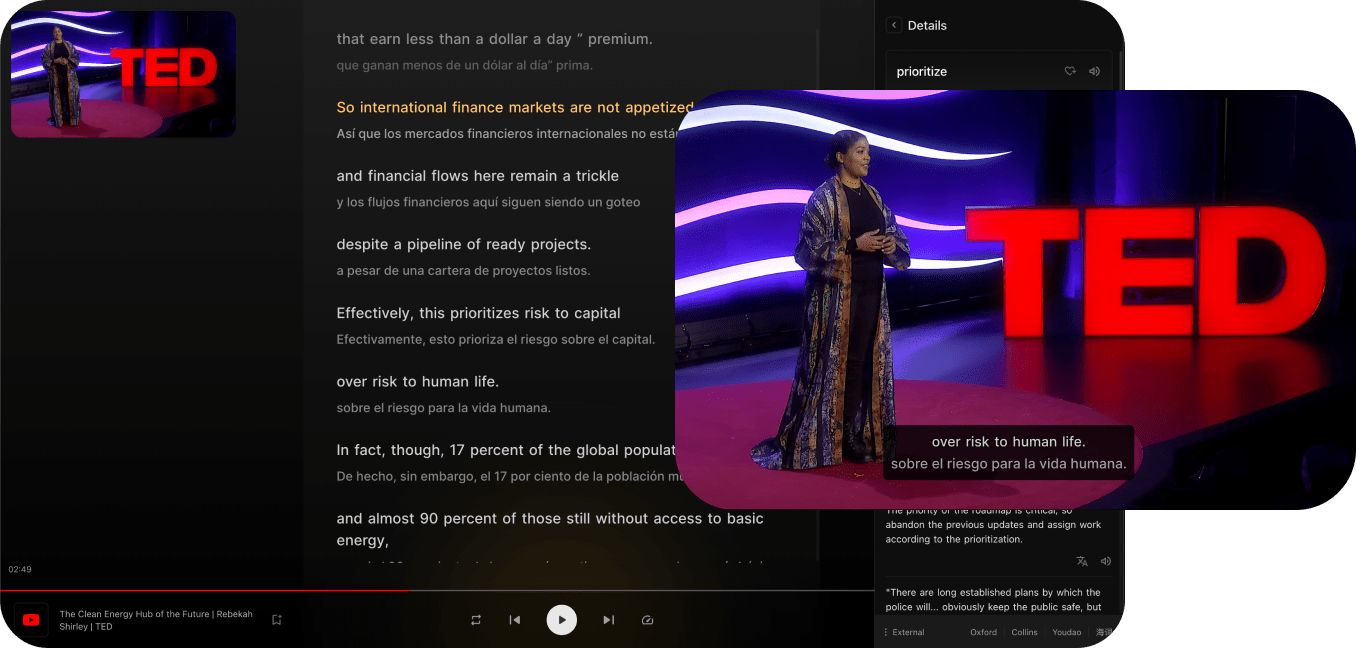
主要なビデオプラットフォームに対応
TrancyはYouTube、Netflix、Udemy、Disney+、TED、edX、Kehan、Courseraなどのプラットフォームにバイリンガル字幕を提供するだけでなく、一般のウェブページでのAIワード/フレーズ翻訳、全文翻訳などの機能も提供します。
全プラットフォームのブラウザに対応
TrancyはiOS Safariブラウザ拡張機能を含む、全プラットフォームで使用できます。
複数の視聴モード
シアターモード、リーディングモード、ミックスモードなど、複数の視聴モードをサポートし、バイリンガル体験を提供します。
複数の練習モード
文のリスニング、スピーキングテスト、選択肢補完、書き取りなど、複数の練習方法をサポートします。
AIビデオサマリー
OpenAIを使用してビデオを要約し、キーポイントを把握します。
AI字幕
たった3〜5分でYouTubeのAI字幕を生成し、正確かつ迅速に提供します。
AI単語定義
字幕内の単語をタップするだけで定義を検索し、AIによる定義を利用できます。
AI文法分析
文を文法的に分析し、文の意味を迅速に理解し、難しい文法をマスターします。
その他のウェブ機能
Trancyはビデオのバイリンガル字幕だけでなく、ウェブページの単語翻訳や全文翻訳などの機能も提供します。